4 Ways to Safeguard Your Credit Union Members From Fraud
Credit unions, with their member-focused approach and community-oriented services, have become increasingly popular. However, they face unique challenges when it comes...
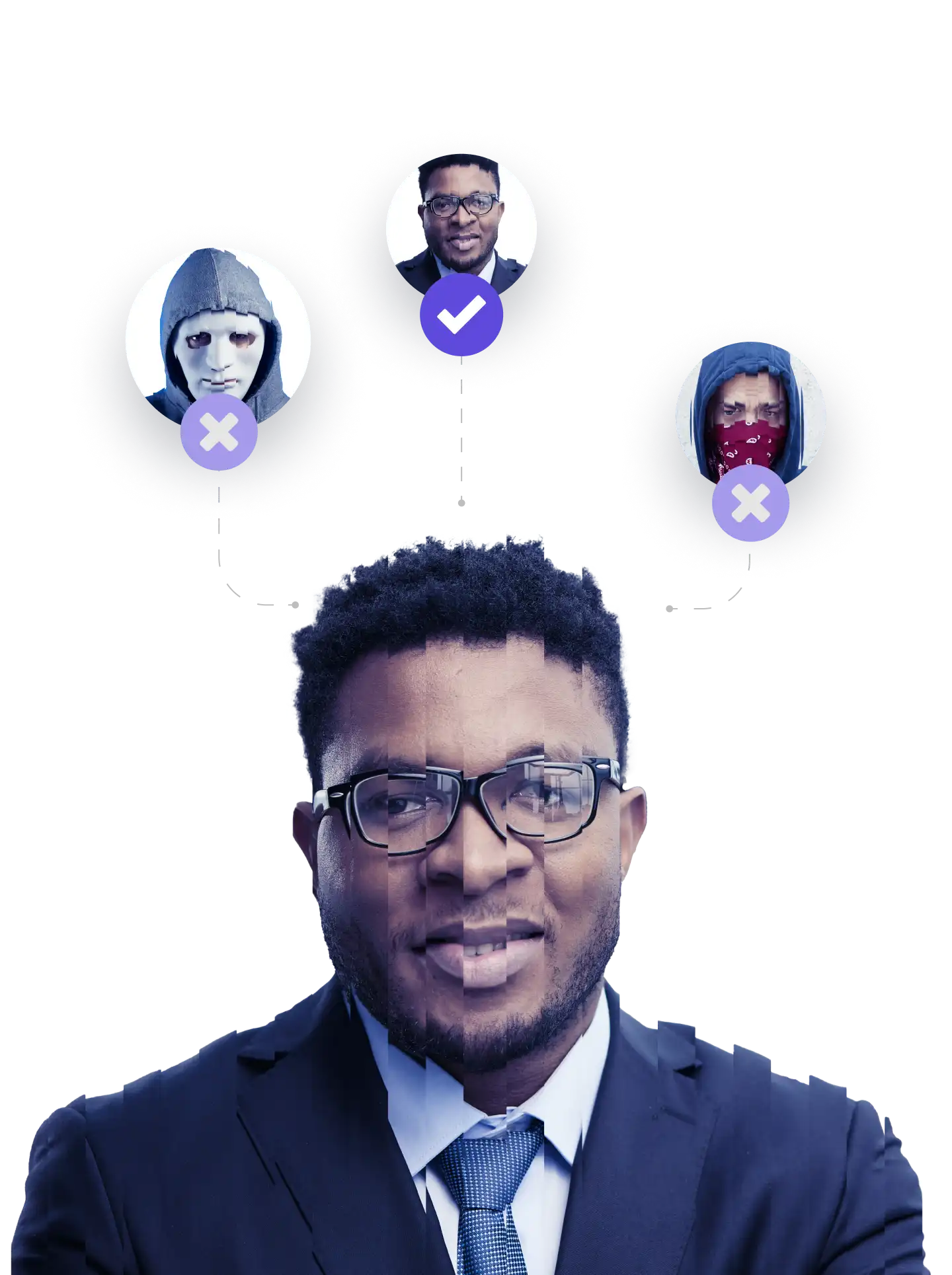
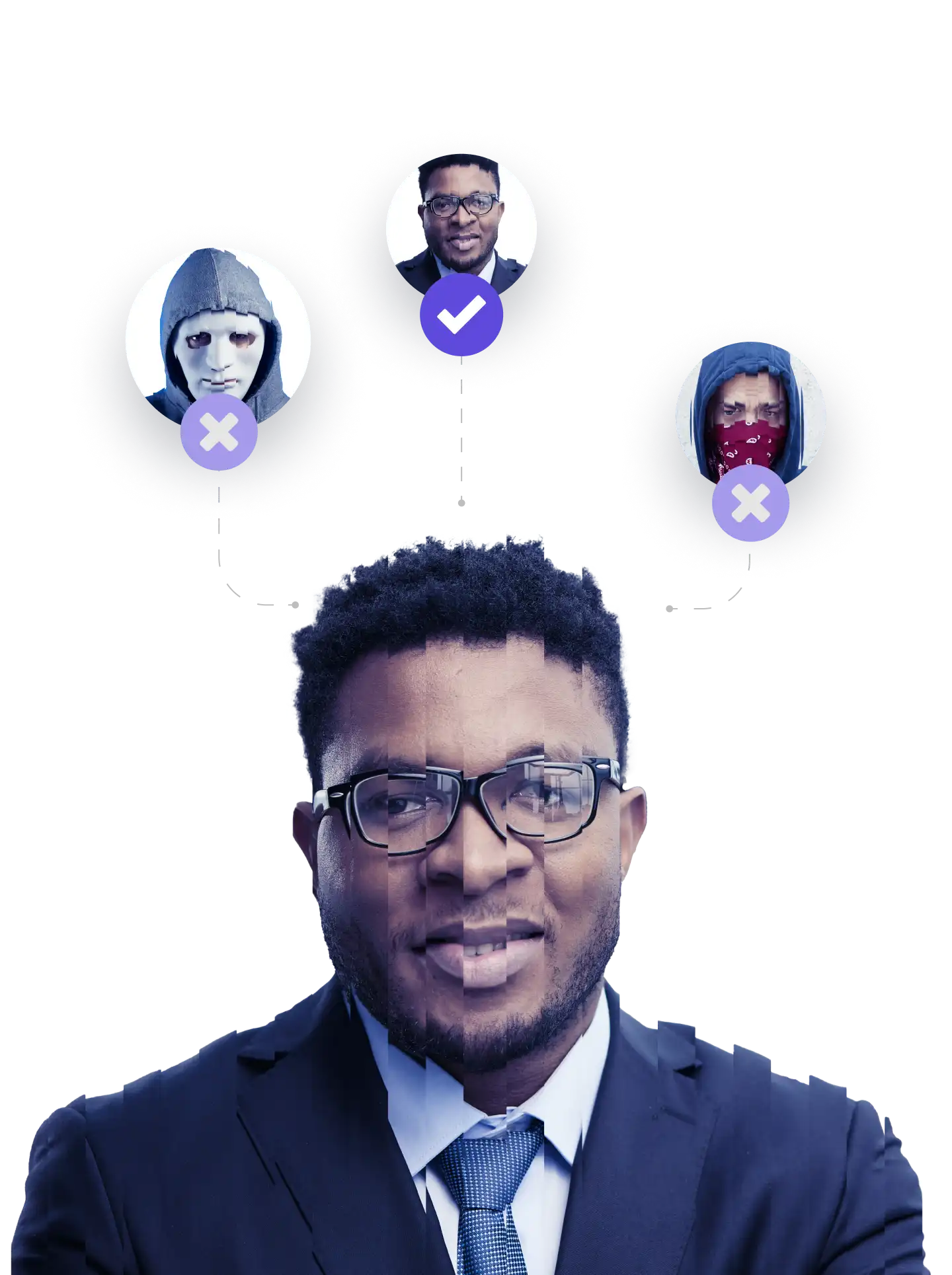
Bid farewell to concerns about transactions being diverted or circumvented by fraudsters and welcome a new age of secure financial transactions with transaction verification. Built on a foundation of privacy, trust, and strong customer authentication, Anonybit ensures that whoever is transacting is who they claim to be. Whether you’re conducting outbound wire transfers, sending or receiving payments, or transacting in other ways, Anonybit ensures that your financial activities are safeguarded at every step through transaction verification. No complicated steps or confusing procedures – just a straightforward, seamless experience for all users.
Secure transaction verification with confidence, unencumbered by tradeoffs between privacy and security.
Capture biometric and conduct liveness checks
Convert biometric into sharded, anonymized bits
Compare the new anonybits against their stored counterparts for an authentication result in milliseconds
Deduplication and Blocklist Checks
Prevent synthetics and known fraudsters from re-enrolling under another name
Call center authentication
Reduce fraud, shorten Average Handling Times and improve the strong customer authentication experience for immediate ROI
Workforce Authentication
Enable seamless access for your team members while ensuring a robust layer of privacy-preserving biometric protection for sensitive corporate data
ANONYBIT GENIE MODULES
The Anonybit Genie is the first integrated identity management system built with privacy-by-design from the ground up. Connecting the user lifecycle from digital onboarding to authentication and beyond with persistent biometrics, Anonybit eliminates passwords, knowledge questions and other weak identifiers and ensures a seamless user experience at all service points – online, in person, in the chat, and on the phone – while maintaining the highest levels of user privacy.
Want to see how it works?
Digital Onboarding
Device Binding
Authentication
Account Recovery
RESOURCES

Get rid of central honeypots of data. Embrace biometrics across the user lifecycle.
